AMI Announces Barcode Support in AptioV UEFI Firmware
NORCROSS, GEORGIA – AMI®, a global leader in powering, managing and securing the world’s connected digital infrastructure through its BIOS, BMC and security solutions, is pleased to announce barcode support in its world class Aptio® V UEFI Firmware.
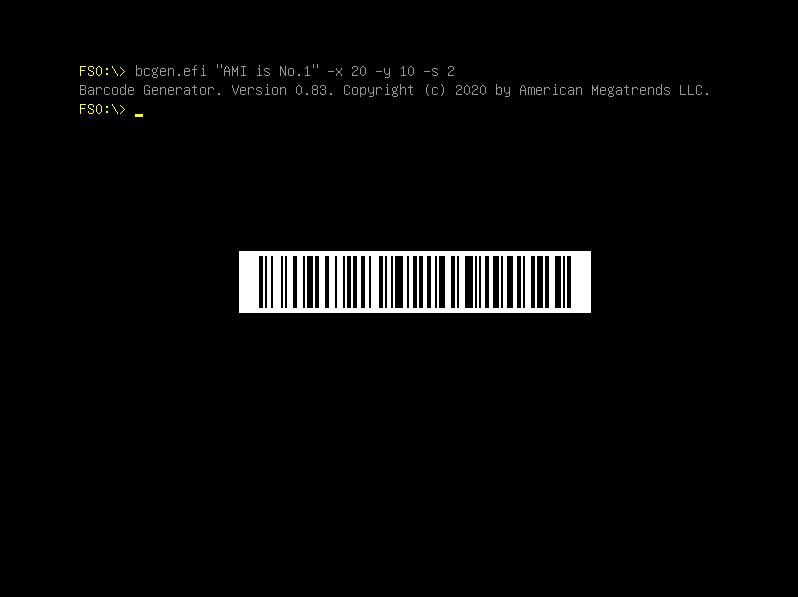
Barcode support allows OEMs and ODMs the ability to encode the computer system serial number, platform ID or other identifiers into the BIOS and display it during system power on.
Barcode technology has been used for decades in manufacturing for inventory control, accuracy and speed. One can typically associate a barcode with the serial number of a device. While serial number inclusion into the firmware has been around for some time, the ability to view the serial number as a barcode is a recent event.
“Passing this information around or recording this data manually could lead to errors. Scanning barcodes using a standard barcode scanner can help eliminate this problem. A barcode scan is not only more reliable, but it takes less time than by hand-entered data,” said Sanjoy Maity, Chief Executive Officer of AMI.
“However, what if the system has no barcode or any type of identifying information on the outside of the device?” he asked.
Hiding Device Identifiers to Reduce Fraud
Serial numbers that were once found on the bottom of laptops and cellular phones, are slowly making their way into the firmware. The reason for this is related to how an OEM’s repair and support contract is structured. If an end-user wants to get support for their device, they typically are required to provide the serial number of their device first. This is a simple way to find out if a device is still covered by a support contract or manufacturer’s warranty.
Large OEMs and ODMs can become targets of fraud perpetrated by non-reputable companies that offer repair and support. These firms can obtain serial numbers by browsing classified listings with the intent to report devices associated with them as being repaired by their facility and requesting compensation for services that they did not render.
While this is one type of fraud, there are others that are not going to be mentioned in this release due to the sensitive nature of the subject. Hiding the serial number offers additional security benefits to the end-user of the device as well.
Obtaining the Serial Number
A device without a serial number printed on the outside of the device needs to be powered on to display the serial number. Traditionally, the serial number would be listed in the BIOS setup menu. If the owner password protects their device, then their serial number would remain secure.
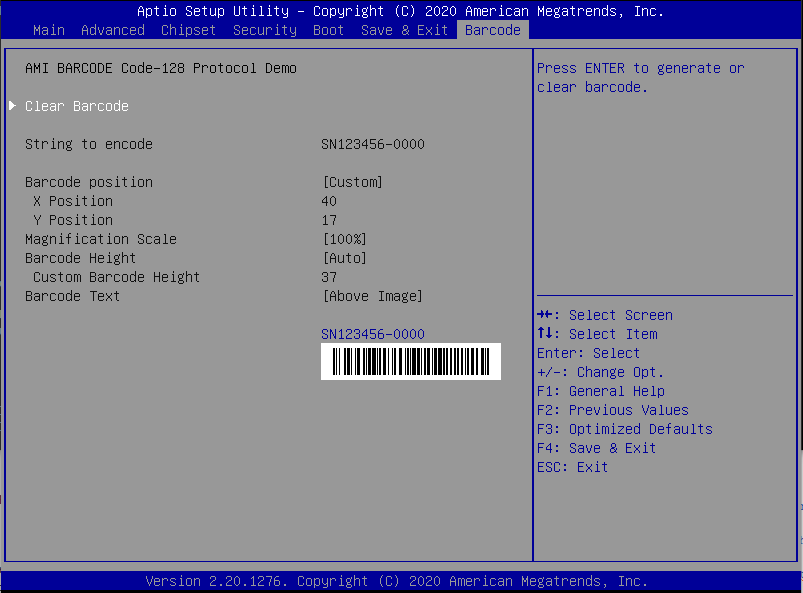
However, obtaining the serial number by powering on the device and going into the BIOS setup menu to view the serial number limits the accuracy and speed of processing the device, whether it is during production, quality control or support of the device.
This is where barcode support in the BIOS has its clear benefit. Barcode support returns accuracy and speed back into the process by allowing the OEM, ODM and its authorized support representatives to quickly bring up the serial number or other platform identifier via a visual barcode, which can be quickly scanned.
For more information on AptioV and all its licensable eModules, please visit ami.com/aptio or call 1-800-828-9264 to speak with an AMI Sales Representative.






