There are many keys (and key combinations) used to enter UEFI BIOS setup.
Just a word of caution before we continue. Do NOT change and save UEFI BIOS settings unless you know what you are doing.
Here are the top three keys used to gain access to the UEFI BIOS setup.
- (or + )

To find out how to enter your system’s BIOS setup, restart your computer. As your system boots up, you may be prompted with a message that states, “Press or to enter setup,” or “Press , and to enter setup.”
If you do not see this message, the BIOS boot screen may be hidden. If it is, consult your manual… or what I do is hit the key during power on to switch the boot screen from Quiet Boot. When Quiet Boot is enabled, the text-based BIOS boot screen is hidden and replaced with the logo, typically the system or motherboard manufacturer logo.

Here is a list of keys and key combinations (including the top three):
- + + keys (some motherboards and option ROMs)
- + + keys (some motherboards and option ROMs)
(UEFI default)- (UEFI default)
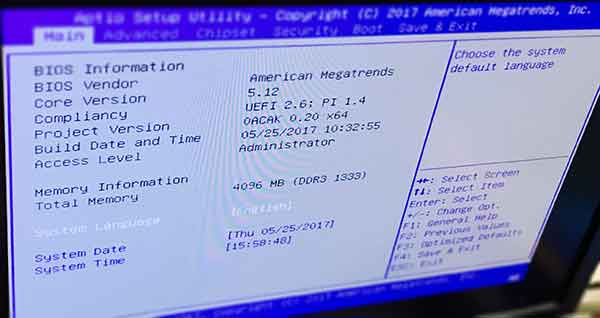
- (some Toshiba notebooks)
ODMs and OEMs that ship with Aptio V (AMI UEFI BIOS firmware) on their platforms, can program the key (or combination of keys) that provide access to UEFI BIOS setup. If you are an ODM or OEM that licenses Aptio V firmware, contact us to learn how to perform this customization.