Tektagon
Rock Solid Platform Root of Trust
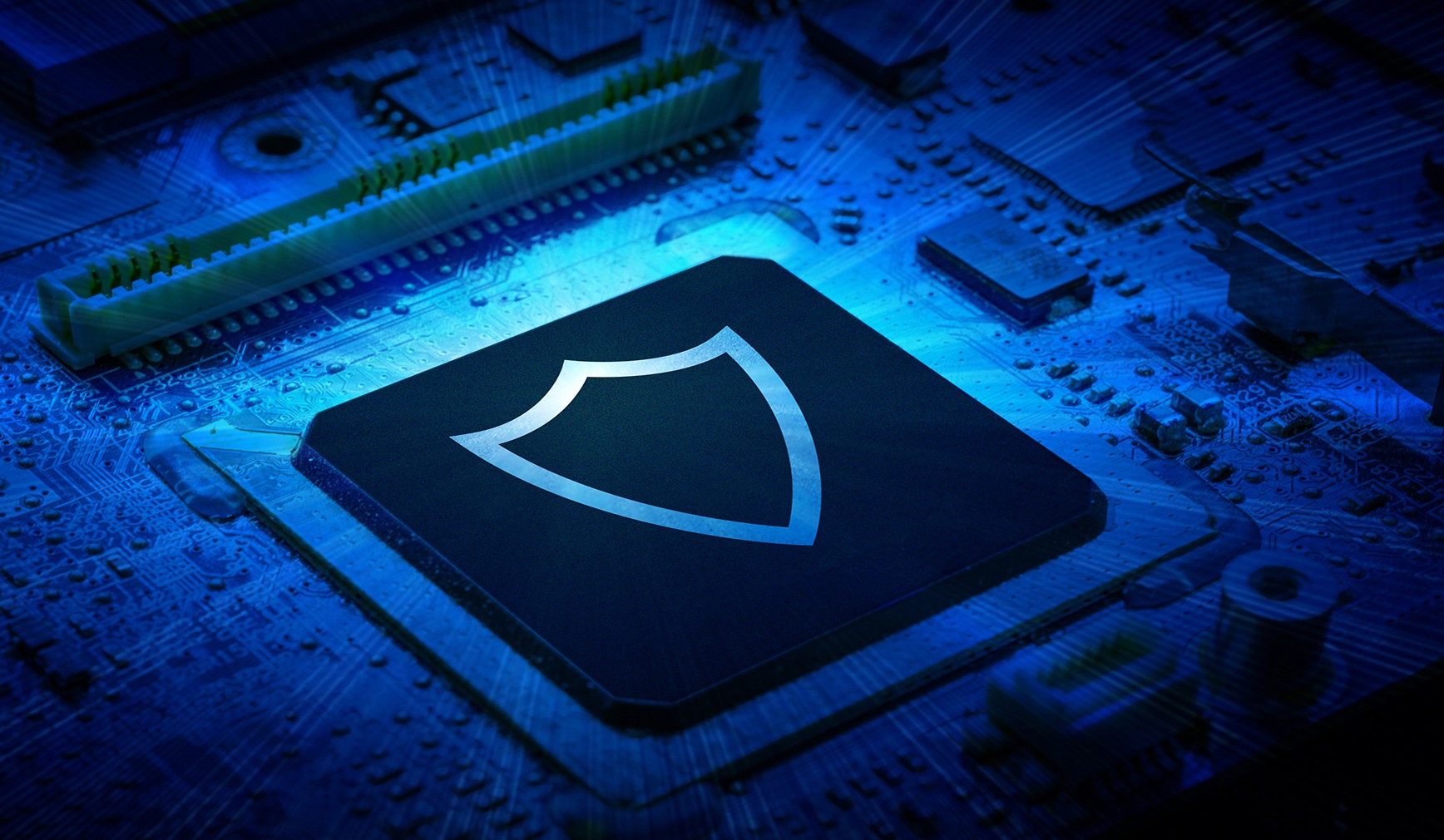
Security isn’t an afterthought. It’s engineered into Tektagon from the ground up. Tektagon delivers protection that’s embedded in silicon, validated in real time and architected for resilience. Its lightweight footprint and modular design enable seamless integration across leading platforms and silicon vendors. With corruption detection at boot, run-time protection and firmware recovery, Tektagon defends your most critical infrastructure without slowing it down.
Delivers T-1 validation with attestation of signed firmware and code-level measurements.
Real-time SPI bus filtering detects unauthorized changes and enforces runtime integrity.
Enables secure updates with anti-tampering workflows and cryptographic validation.
Provides a modular, reusable architecture across Intel, AMD, Arm and NVIDIA platforms.
Supports audit-ready logging, forensic telemetry and recovery safeguards for incident response.
Anchored in Hardware Root of Trust (HRoT) silicon that ensures immutable protection from the first boot onward.
Ensures only authenticated firmware is executed, protecting against code injection, tampering and denial of service attacks from the moment a system powers on.
Proactive Firmware Protection.
In a fast-changing world where cyberattacks can now reach lower points in the stack, Tektagon goes deeper – delivering protection at the firmware level where threats increasingly take root.

More than a firmware safeguard, Tektagon delivers proactive firmware protection for the infrastructure layers attackers increasingly target.

Seamless integration with Aptio and MegaRAC simplifies deployment and expands coverage in high-uptime environments where failure or compromise is not an option.
Tektagon is protection without compromise: resilient, verified and trusted by the world’s leading technology companies.
Seamless Security Across the AMI Firmware Stack
Working in concert with Aptio and MegaRAC, Tektagon secures the full firmware lifecycle from first instruction to runtime recovery. Together, they deliver seamless standards-aligned security across the AMI firmware stack without the need for additional code development. Aptio also integrates security standards like Secure Boot, TPM 2.0, Intel TXT, AMD SEV and platform-specific protections to create a resilient firmware foundation that is ready for tomorrow’s compliance and threat landscape.
But resilience alone isn’t enough – because attackers are constantly evolving. That’s why Tektagon works together with Aptio for layered, lifecycle-spanning protection against even the most sophisticated firmware-based attacks.
Unified platform protection across BIOS, BMC and runtime environments, hardened from boot through operation.
Optimized for AI clusters, edge computing and hybrid environments requiring continuous integrity enforcement.
Relentless Engineering, Real-World Support
From pre-silicon to post-launch, AMI delivers hands-on, expert-led support tailored to our clients’ needs. With global coverage, direct engagement models and deep partnerships across the silicon and OEM ecosystem, our teams work as an extension of yours.

24/7 support with escalation paths for ODMs, OEMs and silicon partners

Integration engineers embedded with customer teams during critical phases
Fewer bugs, faster resolution, less friction


Less Integration, More Innovation.
Tektagon Community Edition: Open Source Platform Root of Trust
Tektagon Community Edition is an open-source Platform Root of Trust (PRoT) solution with foundational firmware security features that detect platform firmware corruption, recover the firmware and protect firmware integrity.